What You Need to Know about Online Payment Fraud in 2023
Learn about the types of payment fraud out there, how they relate to money laundering, and how businesses can safeguard themselves.
Payment fraud is a big problem, and it’s only going to get worse in the coming years. According to Statista, fraudulent transactions using payment cards alone are expected to increase to $38.5 billion by 2027.
Payment fraud prevention, therefore, is paramount for businesses and their clients—not only for anti-money laundering (AML) compliance, but also to protect assets and business reputations. However, it isn’t the simplest of tasks, since fraudsters are constantly looking for new ways to commit payment fraud—whether it’s using social engineering or creating look-alike domains to pose as legitimate vendors.
Let’s dive into payment fraud, ways to prevent it, how to ensure that your business—and your clients—can avoid malicious scams.
What is payment fraud?
Payment fraud is stealing payment information to make unauthorized transactions. There are two broad categories:
- “Card-present” fraud, which occurs when criminals use stolen or counterfeit cards to make purchases in-person (say, at an ATM or brick-and-mortar shop). This has become less common, however, as criminals have mostly turned their attention to online fraud.
- “Card-not-present” fraud, which occurs online. This kind of fraud usually involves unauthorized use of payment information (card number, billing address, CVV and expiration date) to purchase products online—for instance, through e-commerce websites.
How does online payment fraud work?
Step 1: Fraudsters steal your personal information
The first thing that fraudsters need to commit payment fraud is personal information. Here are some ways that they can get their hands on it:
- Social engineering
This is a manipulation technique that involves tricking people into disclosing their sensitive data. This can be when a criminal calls their victim pretending to be a bank representative—using a technique called spoofing—and asks them to confirm their account details, including payment information.
- Phishing
The most common method of social engineering is phishing, which uses emails, phone calls, texts, and social media to gather sensitive personal data from unsuspecting victims. This can be when criminals send an email pretending to be from a legitimate online service, containing a malicious link that fools the victim into entering their login credentials—which leads to account takeover and identity theft.
Suggested read: Identity Theft Explained: How Businesses Can Detect and Prevent It
- Business email compromise (BEC)
This is a complex form of phishing that targets a businesses’ sensitive information and finances. Targets include HR, accounting departments, or even high-level executives like the CFO. The goal is to use social engineering techniques to trick members of an organization into sharing highly-sensitive information or making unauthorized payments.
- Enumeration
Fraudsters can also use a technique called enumeration. This is when hackers determine login credentials using brute-forcing software, which tests numerous combinations to pass the authentication process. Once an account is compromised, hackers can get their hands on sensitive personal information—especially payment details.
Step 2: Fraudsters use your personal information to make unauthorized purchases
Once fraudsters get their hands on personal information, they have multiple ways to commit payment fraud:
- Credit card fraud
If someone’s credit card information is leaked in full, fraudsters can simply commit credit card fraud, which is when unauthorized purchases are made using someone else’s payment information—usually with the aim of obtaining and reselling products.
- Card testing
Full payment details aren’t always available to fraudsters, which opens the door to other payment fraud techniques—such as card testing. This is when fraudsters, in this case known as “carders”, test stolen credit card numbers to see which can be used to make unauthorized purchases. This can either be done manually, where the fraudster checks card validity by making small purchases—or by using special special bots to test large numbers of cards within a short time span, which is known as carding. Proper transaction monitoring tools can help spot carding and card testing attacks ahead of time.
- Triangulation fraud
Triangulation fraud involves three parties—an unaware customer, an online shop, and a fraudster as a middleman. It usually happens as follows: an unsuspecting customer places an order with a fraudulent seller at a legit marketplace (such as Amazon). The fraudulent seller then places an order for the actual product from a legitimate seller using a stolen credit card.
- Online gaming scam
Fraudsters can develop an online game that gets listed on the App Store or Google Play. The players of the game are then asked to pay a small fee in order to continue playing, which enables the fraudsters to eventually extract a much larger amount from the card linked to their Apple ID.
To offer a game on the App Store, it’s necessary to have a bank account. In this case, fraudsters open bank accounts with neobanks and MSBs, rather than with traditional financial institutions. Therefore, fintech companies need a high-quality business verification service (KYB).
Chargeback fraud (aka “friendly fraud”)
Not all payment fraud involves stealing personal information through social engineering and so on. Friendly fraud is when someone makes an intentional purchase online, and then contacts their bank to dispute the charge by falsely claiming that the transaction was invalid. To recognize this kind of fraud, it’s important to monitor customers’ behavioral patterns.
A reliable transaction monitoring tool lets businesses set triggers that detect suspicious transactions, such as purchases made by the same client simultaneously, unusually large transactions (above the AML threshold), and high-risk countries.
Suggested read: A Global Guide to AML Compliance in Gambling, Gaming, and Betting (2023)
Online payment fraud statistics
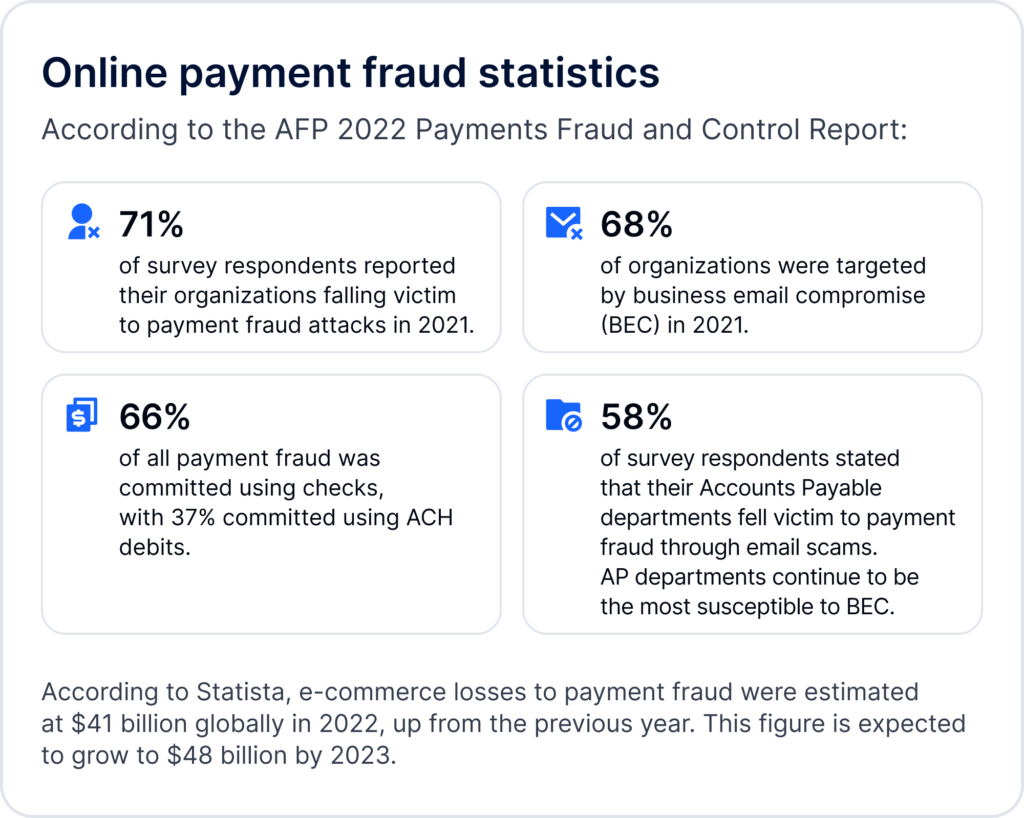
According to the AFP 2022 Payments Fraud and Control Report conducted by JPMorgan:
- 71% of survey respondents reported their organizations had been victims of payment fraud attacks in 2021.
- 68% of organizations were targeted by business email compromise (BEC) in 2021.
- Checks (66%) and ACH debits (37%) were the payment methods most impacted by payment fraud activity.
- Accounts Payable (AP) departments continue to be most susceptible to BEC, with 58% of survey respondents saying their AP departments were compromised through email scams.
According to Statista, e-commerce losses to online payment fraud were estimated at $41 billion globally in 2022, up from the previous year. This figure is expected to grow further to $48 billion in 2023.
Payment fraud and money laundering
Payment fraud is a predicate offense to money laundering (ML). In other words, the proceeds of payment fraud ultimately need to be laundered by fraudsters. This means that payment fraud is a direct contributing factor to instances of money laundering.
Red flags and ways to prevent payment fraud
The following red flags often signal payment fraud:
- Unusual transaction amounts
- Unusual cross-border or international transactions
- Unusual frequency of transactions
- Unusual transaction types
- Recurring refunds
- Unknown chargebacks
- Unfamiliar shipping addresses
- Shipping addresses too far from the IP address
- Errors in ID documents
- Transactions exceeding the account balance or credit limits.
Here’s how to spot the above red flags before it’s too late:
- Taking a risk-based approach towards customer profiles, partners, and vendors
- Cyber-security measures and policies, like using secure VPNs, etc.
- Conducting regular employee training
- Using a reliable KYC solution to onboard only trustworthy users
- Requesting face authentication in cases of unusual activity
- Using a reliable KYB solution to know and trust the partners and corporate customers you work with
- Using a transaction monitoring tool to quickly detect unusual transactions
- Encrypting transactions
- Using up-to-date software.

FAQ
-
What are the different kinds of payment fraud?
Payment fraud includes, but is not limited to, chargeback fraud, card testing, and credit card fraud.
-
What is an example of e-commerce fraud?
Carding is one of the most common examples of e-commerce fraud. It is a type of cybercrime in which fraudsters obtain stolen credit card numbers, check which are valid, and use them to purchase goods or resell them.
-
What is an example of gambling fraud?
Multi-accounting to abuse bonuses is one of the most common types of gambling fraud.
-
How is payment fraud detected?
There are red flags of payment fraud which businesses should be aware of. At the same time, reliable transaction monitoring tools can easily detect suspicious fraudulent transactions.
-
How can you handle fraudulent transactions?
- Collecting information about transactions
- Reporting fraud to authorities
- Protecting your identity, online account and personal documents to avoid fraud in the future
-
How can you avoid online payment fraud?
- Be aware of the latest fraud trends and red flags
- Protect your personal data and online accounts with multi-factor authentication
- Use KYC, KYB, and transaction monitoring tools




